Anonymous, Reliable, Secure VPN
KelVPN is a decentralized, quantum-resistant VPN
service that provides the highest level of protection
for your network connection, including protection
from quantum threats.
We do not collect any personal information about users.
What is a VPN?

Security with VPN
The term VPN (virtual private network) refers to a set of mechanisms used for secure data transmission and privacy protection on the Internet. VPN services act as intermediaries between users and the online environment. They provide secure channels for transmitting information, encrypt data using special cryptographic protocols, and mask device IP addresses.

How does VPN empower?
VPN services help users protect themselves from various cyber threats when using open Wi-Fi networks in public places, and they also help bypass geographical and censorship restrictions, opening access to content from anywhere in the world.

Decentralized VPN
A decentralized VPN is an innovative approach to ensuring security and privacy on the internet. Unlike traditional VPNs, this approach avoids the need for a single central server to process all internet traffic. Instead, the network consists of multiple nodes (peers) that interact directly with each other, providing users with a secure and anonymous connection to the Internet.
The absence of a single distribution center in a decentralized VPN guarantees a higher level of security because eavesdropping or tracking user activity often occurs through a central server. Additionally, a decentralized VPN is more resistant to attacks and blockages as it has no single point of failure. This makes it attractive for use in countries where internet censorship is practiced or in situations where connection reliability is critical.
Installation instructions
KelVPN is a decentralized VPN service that provides quantum-resistant protection for your internet connection. Here's how to get started quickly and easily:

Step 1
Download VPN for your platform.

Step 2
Install the app on your device.

Step 3
Purchase an access key.

Step 4
Choose the country and server.

Who we are
KelVPN is part of the quantum-safe Cellframe Network ecosystem, focused on creating various services using blockchain technologies. The project has its own blockchain network with a native token KEL, traded on popular crypto exchanges UniSwap and PancakeSwap. KEL holders can also join the staking program. KelVPN nodes are responsible not only for validating transactions on the blockchain, but can also act as providers and earn income by providing the service.

Become a KelVPN provider
Technical requirements for nodes are close to the minimum. To become a provider, a user only needs to fulfill a few simple conditions. First of all, a stable Internet connection to the device and a public IP address. Then purchase and lock KEL tokens in the stake, and finally download and configure special software developed by the project team.
Learn more
Hardware solutions
A range of devices for users who need not just security, but true control over their network. Each device is designed with a focus on security, high performance, and usability.
More detailsKelVPN advantages

100% anonymity
The service is built on a distributed model. KelVPN blockchain nodes act as VPN access points. The blockchain-based architecture of the service does not technically allow for the collection and storage of user data. Thanks to this, your privacy always remains reliably protected.

Unique VPN protocol
To connect the user's device to a VPN server, we use our own DAP SDK protocol, which is encrypted under the standard HTTP protocol and, if necessary, can be wrapped in any other. This provides maximum flexibility and compatibility with various networks, ensuring a stable and secure connection under any conditions.

Highest level of security
We guarantee protection against any cyber threats, including quantum computer attacks. We encrypt data using the post-quantum CRYSTALS-Dilithium algorithm and use the quantum-secure Kyber 512 protocol for exchanging secret keys. According to National Institute of Standards and Technology (NIST) forecasts, these mechanisms will only become the generally accepted security standard five years from now, but they are already protecting KelVPN user data today.

Unrestricted access to online resources
KelVPN erases cyber borders and gives users freedom of action in the internet space. We provide access to any internet resources from anywhere in the world, regardless of geographical and censorship barriers. Thanks to this technology, VPN users get full access to information and entertainment, regardless of location.

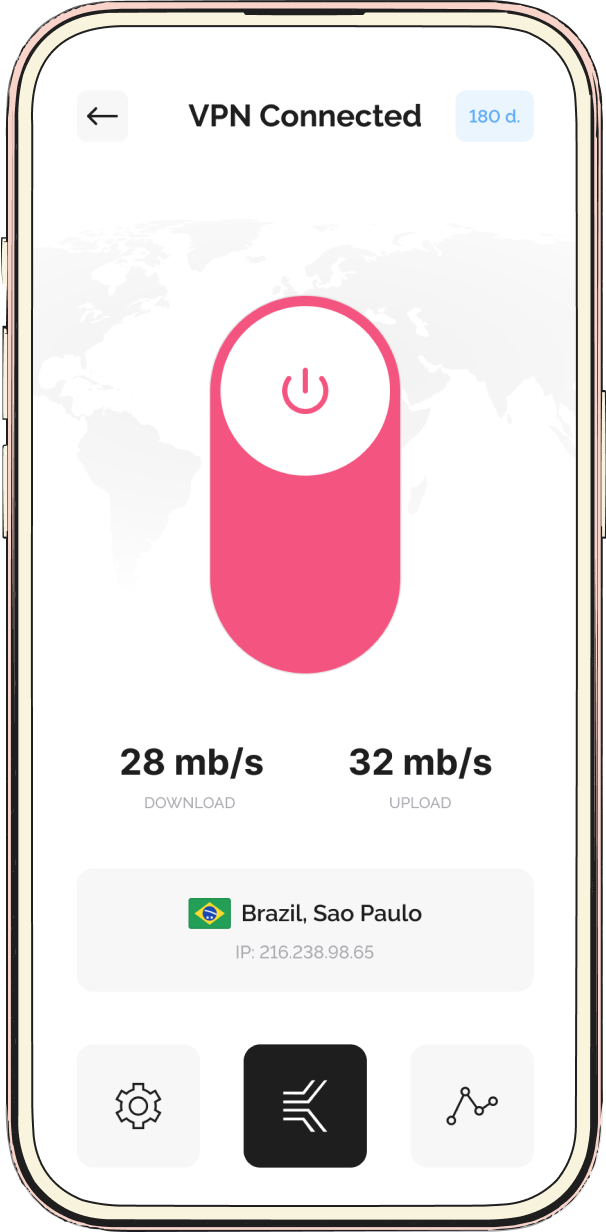
Maximum connection speed
The distributed model of the service provides multiple VPN servers around the world. Anyone can launch our master node and become a VPN provider, and the user only needs to select the nearest access point. This mechanism significantly increases the connection speed, reducing the "last mile".

Payment convenience
For your convenience, we have provided various payment options for the VPN service subscription. Choose the one that suits you best. You can pay for VPN services using KEL tokens - the native currency of the KelVPN project's blockchain network.
Transparent price
In 3 steps you have
- Decentralized service
- Purchase and usage, protected from de-anonymization
- Quantum-resistant encryption
In 3 steps you have
- Decentralized service
- Purchase and usage, protected from de-anonymization
- Quantum-resistant encryption
FAQ
Why should I use a VPN?
Why is a paid VPN better than a free VPN?
On which devices can I install the VPN application?
Which versions of Windows does your VPN support?
Which versions of Linux does your VPN support?
Which versions of Mac OS does your VPN support?
Which versions of Android does your VPN support?
Does VPN slow down the connection speed?
How can I ensure security when using public Wi-Fi networks?
What user data does the VPN store?
Can I use a VPN in a country where access to certain websites and services is prohibited?


